What a fractional CISO actually does (and does not do) at a Series A startup
The most expensive fractional Chief Information Security Officer (CISO) engagement I have seen was not the most expensive one. It cost $4,500 a month, ran for eight months, and produced a 47-page gap assessment, a polished policy library, and a roadmap the engineering team never had time to execute. The CTO paid $36,000 to learn that recommendations without implementation are expensive homework.
I think about that engagement every time a founder asks me what a fractional CISO actually does. The honest answer is that the role can mean two different things, and the difference between them is the difference between a working security program and an unread PDF. This post is about that difference: what the role actually delivers in a typical month, where most engagements quietly fail, and how to tell whether you are hiring an executor or an advisor before you sign.
What this role is, and the framing that keeps tripping founders up
A fractional CISO is senior security leadership delivered on a structured monthly cadence. Not an employee. Not a consultant. A function that runs whether you think about it that month or not.
At Series A, the engagement is typically 10 to 20 hours per month. Not per week. This is the single most common confusion I see in founder conversations. Most articles describing fractional engagements quote “8 to 16 hours per week,” which is mid-market framing for companies in the 100 to 500 employee range. At a Series A startup with 15 to 60 employees, the standard retainer buys roughly one focused half-day per week, sometimes a full day at the upper end of the range.
Pricing reflects that allocation. Published industry pricing guides place Series A fractional retainers in the $3,000 to $8,000 per month range, depending on scope and framework count. The IANS / Artico Search 2025 CISO Compensation Benchmark puts small-company CISO cash comp at $260,000 annually, with total comp averaging $415,000 once equity is included. That is before recruiting fees and a three-to-six month ramp. The fractional model trades hours for seniority.
The trade is only worth it if those hours go toward work that gets done. Which is where most engagements break.
A typical month, with the work that actually fills the calendar
Here is what a real month looks like for a Series A healthtech company in the middle of a SOC 2 (System and Organization Controls 2) Type II observation window, with an active HIPAA (Health Insurance Portability and Accountability Act) program, two hospital partners, and a few enterprise deals in procurement.
Policy maintenance runs throughout the month. The information security policy gets reviewed against changes to the environment. The acceptable use policy gets updated when a new SaaS tool comes into scope. The incident response plan gets a tabletop walk-through every quarter.
Evidence collection oversight is the work that keeps a SOC 2 observation window from becoming a fire drill in month five. Every week, I pull access logs from the identity provider and confirm provisioning and de-provisioning events have the required approvals. I check change management records and flag any infrastructure change that did not get a ticket while the context is still fresh. I confirm the vulnerability scan cadence ran. None of this is glamorous. All of it is what an auditor looks for during a Type II review against the trust services criteria.
Vendor risk reviews happen as new tools come in, plus a quarterly cycle for high-risk ones. A typical Series A healthtech company onboards three to six new SaaS tools per quarter. Each one needs a brief assessment: what data it touches, whether it requires a Business Associate Agreement (BAA), and where it sits in the risk register.
Security questionnaires are the workload that surprises founders most. A health system or enterprise prospect sends a 120 to 200 question assessment. About 70% of the answers come straight from a maintained response library. The rest need framework-specific tailoring or a 15-minute conversation with engineering to confirm an architecture detail. I have written about this work in more depth in the security questionnaire playbook.
Regulatory monitoring sounds passive. In practice, it is active triage. The Office for Civil Rights (OCR) publishes guidance, the proposed HIPAA 2026 rule continues through rulemaking, state-level privacy laws keep changing. The work is filtering what matters for the specific company and flagging it for the CTO with a recommendation, not a 40-page summary.
Board updates happen quarterly: risk summary, program status, open items, decisions the board needs to make. A short written brief the CEO can forward to investors without modification.
The Umbrex fractional CISO playbook suggests at least 60% of hours should go to governance, tooling strategy, and program work, with firefighting capped at 15%. That matches what I see in healthy engagements. When firefighting eats more, something upstream is broken.
What a fractional CISO does not do, on purpose
This section is where most fractional CISO content gets evasive. The role has clear boundaries, and pretending otherwise is how founder expectations end up misaligned three months into an engagement.
Penetration testing is not part of the retainer. I scope the test, select the vendor, brief them on the architecture, and review the findings. I do not run the test. That requires a specialized firm with its own tooling, methodology, and liability coverage. Budget separately: in my experience, a focused application and infrastructure pen test for a Series A startup runs $10,000 to $30,000, consistent with the ranges in published industry pricing.
Twenty-four-hour incident monitoring is also not part of the retainer. If a security alert fires at 2am, a Managed Security Service Provider (MSSP) handles triage, first response, and the escalation decision. I lead the response when an incident is declared, which means executive decision-making, external communications, regulatory notification, and audit-trail discipline. The split is intentional: you want different people on the alert queue than the ones briefing your board.
Day-to-day information technology (IT) work is not security leadership. Configuring a firewall rule, resetting a Multi-Factor Authentication (MFA) token, debugging a virtual private network connection: these are IT operations. A fractional CISO can advise on the architecture and review the configuration, but routing IT tickets to that calendar is how you turn 20 hours of senior security leadership into 20 hours of help desk.
People management is also out. I will advise on team structure, help write the job description for the future full-time security hire, and sit on the interview panel. I am not managing engineers’ day-to-day work.
None of these exclusions are gaps. They are role architecture. The right Series A program pairs a fractional CISO as executive decision-maker with an MSSP for monitoring, a specialist firm for periodic penetration testing, and a compliance platform such as Vanta or Drata for evidence management. The combination is complete. The fractional CISO alone was never meant to be.
The advisory-only problem
Here is the part almost nobody writes about publicly, and the reason the $36,000 gap assessment from the opening exists.
A meaningful share of the fractional CISO market sells advisory-only engagements. The model looks identical from the outside: monthly retainer, executive-level practitioner, named-CISO experience, a recurring meeting. What is different is who does the work.
In an advisory-only engagement, the fractional CISO reviews your posture, writes recommendations, and produces deliverables that describe what should happen: policy templates, gap reports, roadmaps with target dates. Your engineering team is expected to implement. If you have a four-person engineering team shipping product against a Series A roadmap, those recommendations do not get implemented. The controls “recommended” in month two are still “in progress” in month nine. You pay the retainer the whole way.
Even SideChannel’s published pricing guide acknowledges the split: “A vCISO sets the strategy. Someone has to execute it.” At a Series A startup, the only “someone” available is the engineering team already behind on the roadmap.
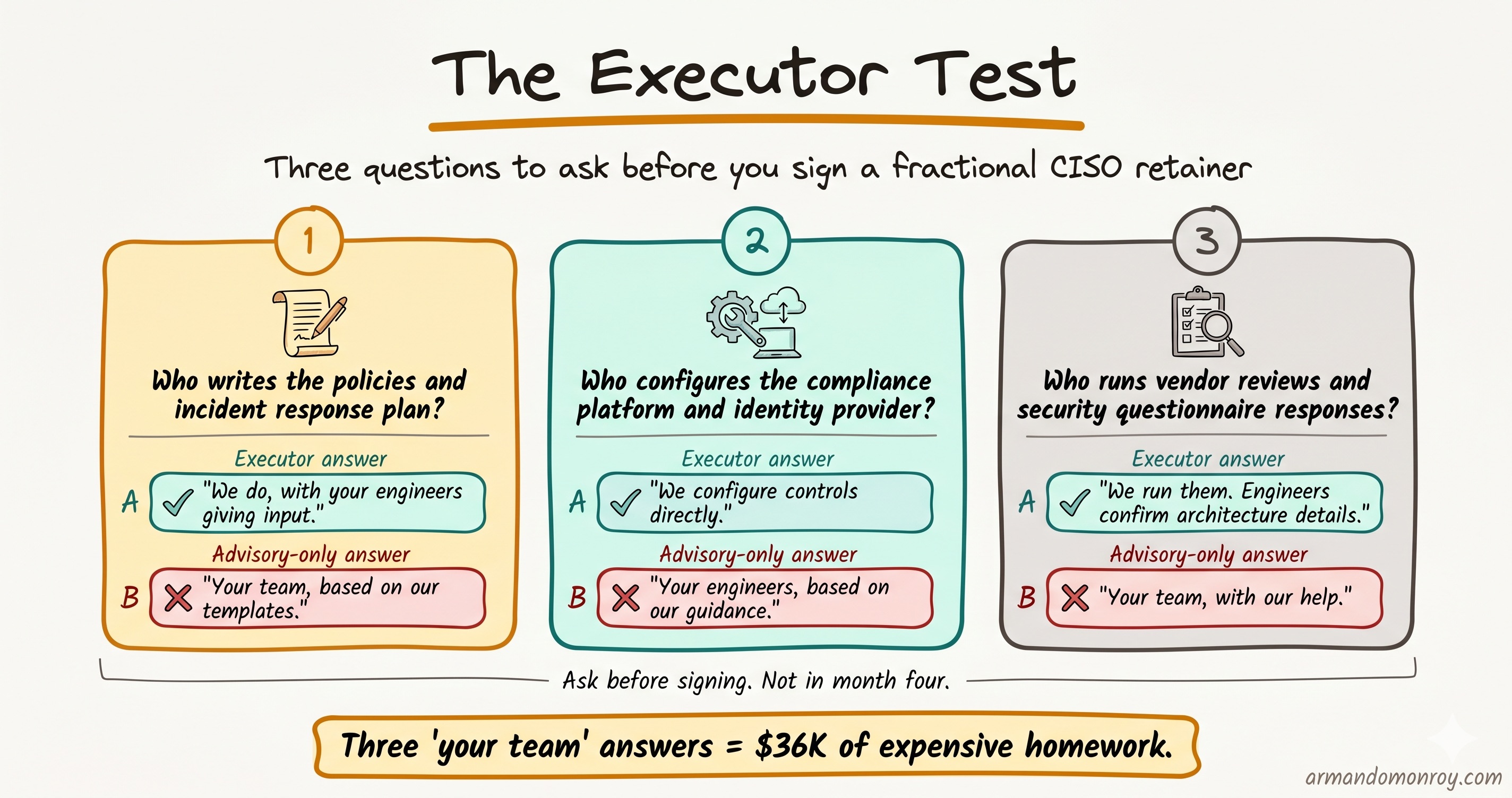
The test to apply before signing is short. Ask three questions:
- Who writes the information security policy and the incident response plan? You, or my engineering team based on your templates?
- Who configures the controls in the compliance platform and the identity provider? You, or my engineering team based on your guidance?
- Who runs the vendor risk reviews and the security questionnaire responses? You, or my engineering team with your help?
If the answer to all three is “your team, based on our recommendations,” the engagement is advisory-only. That model can work for a company that already has an internal security or compliance function. At Series A, you do not. The answer needs to be “we do, with your engineers providing context, access, and the occasional architectural decision.”
This is not a question about how the proposal is written. It is a question about who is doing the work in month four. Ask it before signing.
When to graduate to full-time
A good fractional CISO tells you when the model will stop working for you. That conversation should happen before you need it to.
The signals are not just headcount, though headcount is the easiest proxy. Across the Help Net Security interview with Nikoloz Kokhreidze, the IANS data, and what I see in practice, the transition is driven more by obligation density than employee count. A 60-person startup with SOC 2 Type II renewal, a HIPAA audit cycle, HITRUST CSF (Health Information Trust Alliance Common Security Framework) work in progress, and an active Series B security review at the same time has outgrown the model. A 180-person startup with a single mature SOC 2 program has not. Under 200 employees and one or two frameworks, the model usually still fits. Three or more frameworks in parallel, active regulatory examination, or merger and acquisition integration means it is time to plan the full-time hire. Investors typically start asking the question around Series C anyway.
The transition itself should not be a disruption. By the time you hire full-time, the fractional engagement should have produced a documented program, a maintained evidence base, a working compliance platform configuration, and a job description the new hire can step into. Starting the program over when the full-time CISO arrives means the fractional engagement did not do its job.
The takeaway
The question is not whether to hire a fractional CISO. It is whether you are hiring one who will do the work or one who will tell you what work needs to be done. At Series A, you do not have an internal team to receive recommendations. You need someone in the program, not above it.