What a 12-week SOC 2 + HIPAA timeline actually looks like for a Series A healthtech startup
Last month a CTO asked me to review the compliance timeline his team had put together. It was a neat two-page spreadsheet. Twelve weeks, start to finish, ending with “SOC 2 report delivered to customer.” I asked him if he knew what a Type II observation period was. He did not. His spreadsheet had him handing a report to a health system three months before one could possibly exist.
This is the most common planning mistake I see at Series A healthtech companies. The question “how long does SOC 2 take?” is the wrong starting point. The right question is: when do I need a report in a customer’s hands, and what does that mean I need to start today?
Here is what a realistic 12-week timeline covers, what it does not cover, and how to keep your engineering team from becoming a compliance shop.
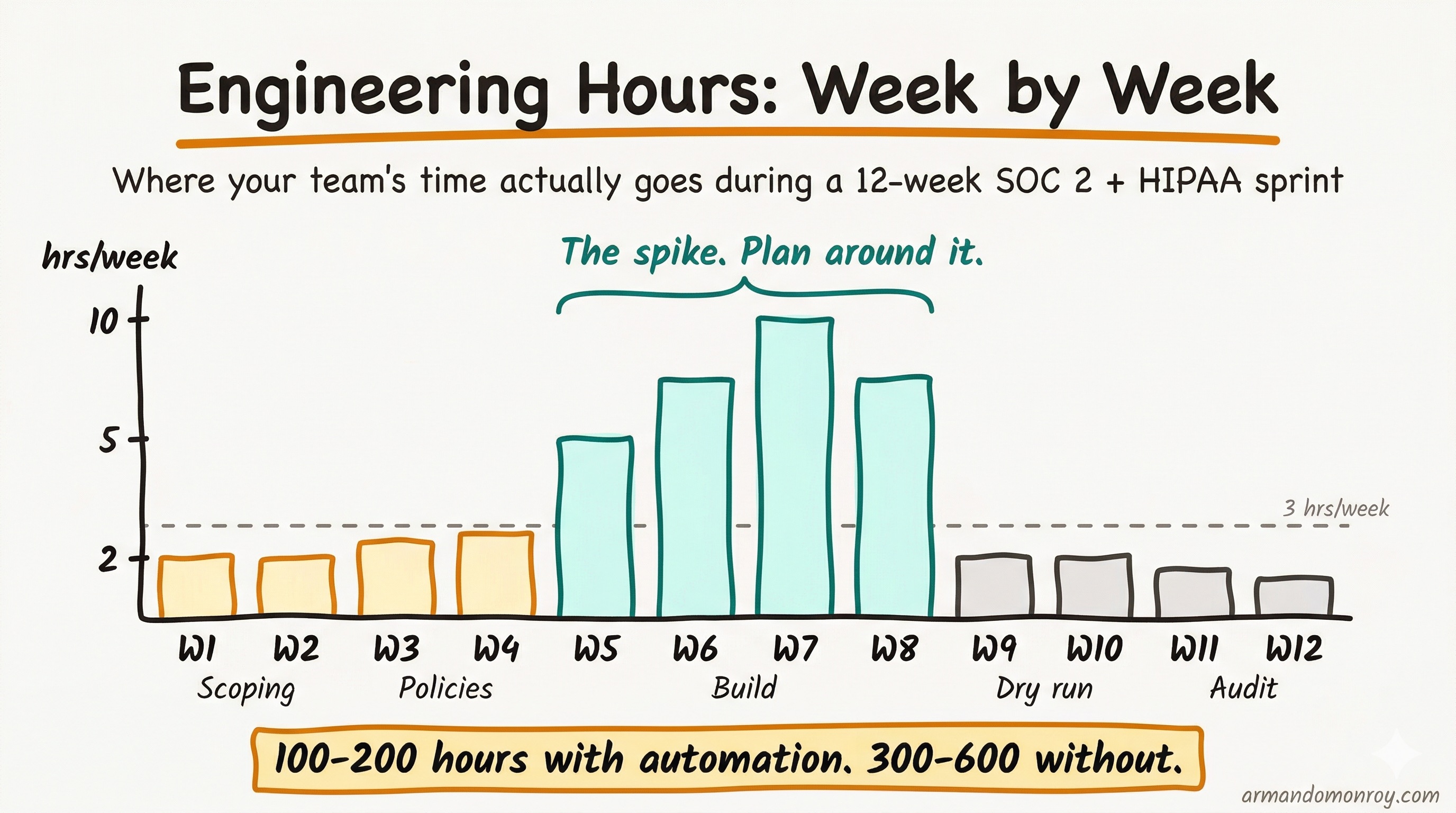
TL;DR: Twelve weeks of focused work gets you a SOC 2 Type I report and a HIPAA compliance program that can survive customer scrutiny, but your Type II report (the one buyers actually want) arrives around month seven or eight because of the observation period. Engineering time drops to under 3 hours per week after Week 8. Running both frameworks together instead of sequentially saves 4 to 6 weeks of redundant work.
What 12 weeks actually gets you
Let me be specific about scope. Twelve weeks of focused work gets you to two things: a SOC 2 Type I report (a point-in-time snapshot of your controls) and a HIPAA compliance program that can withstand scrutiny from a health system’s security team.
What it does not get you is a SOC 2 Type II report. That requires a minimum three-month observation period where your controls operate continuously, and the clock on that period starts at Week 1. So the Type II report, the one enterprise buyers actually want, lands around month seven or eight from the day you begin. Planning for that timeline is the single most important thing you can do before touching a policy document.
Why you should run both frameworks together
The instinct is to do SOC 2 first, then tackle HIPAA later. That instinct costs you an extra four to six weeks of redundant work. A cross-mapping analysis by Censinet found that roughly 65% of HIPAA Security Rule controls overlap with SOC 2 Security criteria. Access control, encryption, audit logging, incident response, vendor risk management: you build these once and map them to both frameworks.
Running both together compresses what would otherwise be a 9-to-12-month sequential effort into 4 to 5 months. The overlap is real, but so are the differences. SOC 2 does not cover HIPAA’s Breach Notification Rule, Privacy Rule requirements, Business Associate Agreements (BAAs), or electronic protected health information (ePHI) data flow mapping. Those are separate workstreams that run in parallel during this timeline.
The week-by-week breakdown
Here is the full timeline at a glance before I walk through each phase.
| Phase | Weeks | Focus | Engineering Time |
|---|---|---|---|
| Gap analysis & scoping | 1-2 | Framework mapping, ePHI data flow, auditor selection | 3-5 hours total |
| Policy writing & control design | 3-4 | Policies, control matrix, BAA inventory | 4-6 hours total |
| Control implementation | 5-8 | Technical controls, monitoring, evidence collection | 5-10 hours/week |
| Internal readiness review | 9-10 | Dry run, remediation, evidence packaging | 3-4 hours total |
| Audit engagement | 11-12 | Type I fieldwork, evidence submission | 2-3 hours total |
Weeks 1-2: Gap analysis and scoping
This is the diagnostic phase. You are answering three questions: what controls do we already have in place, what do we need, and which specific SOC 2 Trust Service Criteria and HIPAA Security Rule specifications apply to our environment?
The concrete deliverables here are a gap assessment against both frameworks, a scoping document that defines your system boundaries (which cloud accounts, which applications, which data stores contain PHI), and an ePHI data flow map. That last one is critical. I have watched teams get to Week 5 before realizing they never mapped where PHI actually lives, and it forced a restart of their control design. On one engagement, the data flow map revealed that a third-party analytics tool was ingesting patient identifiers through event properties that nobody on the engineering team knew about. That single finding changed the entire scope of the project.
This phase also includes selecting your compliance automation platform and your auditor. Book the auditor now, not in Week 9. Specialist SOC 2 firms deliver reports in 2 to 8 weeks after fieldwork, but they book engagements 2 to 3 months in advance. Mid-tier firms can take 2 to 6 months. If you wait until you feel “ready” to start looking, you will add 6 to 10 weeks to your timeline just waiting for availability.
Engineering time this phase: 3 to 5 hours total for architecture walkthroughs and access inventory.
Weeks 3-4: Policy writing and control design
This is where the bulk of the intellectual work happens, and it is the phase that should absolutely not fall on the CTO. Policy writing is not engineering work. It requires someone who understands both the framework requirements and your actual operating environment, then translates between the two.
The deliverables are your information security policy set (typically 15 to 20 policies covering access control, data classification, incident response, change management, and vendor management), your control matrix mapping each control to its SOC 2 criteria and HIPAA specification, and your BAA templates and inventory.
The biggest failure mode here is using policy templates that do not match your actual practices. An access control policy that says “all access requires manager approval via ticketing system” is useless if your team actually manages access through Slack messages and ad-hoc Terraform changes. The policy has to describe what you actually do, or what you are committed to doing starting now.
Engineering time this phase: 4 to 6 hours total for reviewing policies against actual workflows.
Weeks 5-8: Control implementation and evidence collection
Now the engineering team gets involved in a meaningful way. This is the technical build phase: configuring cloud infrastructure controls, setting up continuous monitoring, integrating your compliance platform with your cloud provider and CI/CD pipeline, and generating the evidence trail that auditors need.
Specific technical work includes: enforcing multi-factor authentication (MFA) across every system that touches ePHI, configuring audit logging, implementing automated access reviews, setting up vulnerability scanning, encrypting data at rest and in transit across all environments (including staging), and establishing change management so that every production deploy has a traceable approval.
This is the most time-intensive phase for your engineering team. The “3 hours per week” number that gets thrown around is realistic after Week 8, but during this phase, expect closer to 5 to 10 hours per week from your lead engineer. With a compliance automation platform, total team hours across the full project run 100 to 200. Without one, you are looking at 300 to 600 hours. The platform is not optional at a startup where engineering capacity is your most constrained resource.
One critical note: your SOC 2 Type II observation period starts as soon as your controls are operating. Many teams make the mistake of starting the observation period before MFA is fully enforced or before audit logging is configured everywhere. I worked with one team that kicked off their observation window while quarterly access reviews were still “planned but not yet running.” Six weeks in, the auditor flagged it, and they had to restart the clock from scratch. If an auditor finds that a control was not operating for the first three weeks of your observation window, you either get an exception in your report (which customers notice) or you restart the window.
Engineering time this phase: 5 to 10 hours per week for the lead engineer, 2 to 3 hours per week for other team members involved in specific implementations.
Weeks 9-10: Internal readiness review
This is your dry run. Before an auditor looks at anything, you walk through every control, every piece of evidence, and every policy to verify they are consistent, current, and complete.
The deliverables are a readiness assessment report, a remediation plan for gaps found, and a completed evidence package organized by SOC 2 criteria and HIPAA specification.
Schedule your penetration test at the start of this project, not during this phase. Pen testing vendors typically book 4 to 6 weeks out, and you want results in hand by Week 9 so you have time to remediate any findings. If you schedule the pen test in Week 9, you will not get results until Week 11 at the earliest, and any critical findings will push your audit engagement back.
Engineering time this phase: 3 to 4 hours total for evidence verification and answering follow-up questions.
Weeks 11-12: Audit engagement and evidence submission
If you did the previous phases well, this is the quietest part of the timeline. The auditor conducts Type I fieldwork (testing that your controls are designed and implemented as described at a point in time), reviews your evidence, and asks clarifying questions.
For combined SOC 2 and HIPAA, audit fees typically range from $30,000 to $75,000, depending on scope, auditor, and whether you are doing SOC 2 only or a combined engagement. A SOC 2 Type I on its own runs $10,000 to $20,000.
Remediation for any findings can take anywhere from 10 days to 3 months, so the cleaner your readiness review in Weeks 9-10, the faster this phase closes.
Engineering time this phase: 2 to 3 hours total, mostly answering auditor questions.
What automation handles and what it does not
Compliance platforms (Vanta, Drata, Sprinto, and others) automate the repetitive parts: pulling evidence from your cloud provider, monitoring for configuration drift, tracking policy acknowledgments, and generating auditor-ready evidence packages.
What they do not automate: scoping decisions, risk appetite conversations, policy customization, ePHI data flow mapping, and BAA chain verification. These require judgment, context about your specific product, and someone who understands the regulatory intent behind each requirement. I once traced a BAA chain for a client and found that their cloud hosting provider had a BAA with them, but the managed database service running inside that provider did not. No platform would have caught that; it took a manual read of three contracts to find the gap.
A compliance platform is a necessary tool. It is not a substitute for someone who knows what they are building.
A note on the incoming HIPAA Security Rule changes
If you are building a HIPAA compliance program right now, you should be aware that the Department of Health and Human Services (HHS) published a Notice of Proposed Rulemaking (NPRM) in January 2025 that would eliminate the distinction between “addressable” and “required” controls. MFA, encryption, annual penetration testing, and biannual vulnerability scanning would all become mandatory with no exceptions.
As of April 2026, this rule has not been finalized. It remains on HHS’s regulatory agenda with a target of May 2026 and a 240-day compliance window after that. I wrote a detailed breakdown of what these changes mean for your engineering team, including the new encryption, MFA, and patch management requirements. Regardless of the final rule’s status, I would build your program as though these controls are required. Your enterprise customers already expect them, and the Office for Civil Rights (OCR) has been actively enforcing security risk analysis requirements, with seven enforcement actions in the first six months of their latest initiative.
Build for where the regulation is going, not where it was.
The real timeline to plan around
Here is the honest math. Twelve weeks gets you audit-ready. Add 3 months for the Type II observation period. Add 2 to 8 weeks for the auditor to deliver the report. Your first SOC 2 Type II report, the one enterprise buyers actually require, arrives roughly 7 to 8 months from the day you start.
If a health system asks you for a Type II report today and you have not started, you are telling them to wait until Q4. That is the conversation every CTO should have with their sales team before a deal depends on it.